Industry 4.0 What is RFID? - Definition & Function in detail
Radio Frequency Identification (RFID) chips have become essential in industry. Here you can find out what RFID means and how communication between transponder and reader works in detail.
Related Vendors


What is RFID? A definition
Radio Frequency Identification is a type of communication between a transmitter (transponder or tag) and a receiver (reader). The system works fully automatically and is used for contactless communication, identification and localisation of objects such as goods, medicines, vehicles or living beings. RFID therefore also falls under the keyword Auto-ID (Automatic Identification and Data Acquisition). For successful use, a transmitter, a receiver, energy and a certain distance are required. In logistics, technology perfects and simplifies processes and ensures a fast movement of materials. Process optimisation in intralogistics using RFID is also largely standard today, so the technology is an essential element for the success of logistics 4.0. Despite the many advantages, the opportunities and limitations of UHF transponders should always be weighed up.
Functionality of Radio Frequency Identification: The Transponder
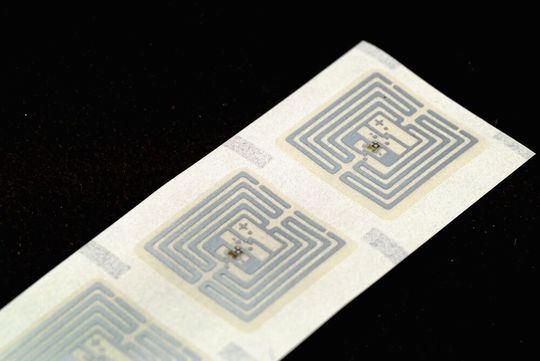
The RFID transmitter is called a transponder, sometimes also a tag or simply a radio tag. It consists of an antenna (often a coil), a computer chip and a carrier material or housing. The chip is equipped with analog and digital circuits, and it also has a memory that can sometimes be written to several times. In some cases, the transponder is a semiconductor chip. Tags differ in several factors. Among other things, they have different sizes, lifetimes, clock frequencies, memory sizes or ranges.
The chips have a unique identity in the form of a serial number so that they can be clearly identified. The identity cannot be changed, which can prevent abuse. If it is a rewritable memory, the identity can be extended continuously and fully automatically by additional information (Auto-ID). In this respect, for example, previous locations of goods are interesting. RFID technology is also essential when it comes to choosing the right order picking procedure.
Tags usually do not have their own energy supply. In this case, the transponder is called passive. The reader delivers the necessary energy for data transmission to the tag. The antenna must be a coil that charges a capacitor by induction. Exceptions called active transponders have their own battery. Their use is worth it if the tag is to have a long range and various additional functions.
Transponders can be attached to or in the object to be marked. For example, they are stuck on (e.g. on pallets or cartons), embedded directly in objects (e.g. in screws, shoe soles, banknotes or documents) and even implanted in living beings (in pets behind the ear, in people's hands). Successful research and development have made it possible to use temperature-resistant transponders since 2006. Since then, they can even be cast in metals, which has various advantages: the risk of damage, wear and tear or loss is minimised and they are also invisible.
Functionality of Radio Frequency Identification: The Reader
A reader that must be in close range reads the tag's data using an alternating electromagnetic field or high-frequency radio waves. The receiver is also known as a reader. In addition to purely readout readers, there are also readers that can write new information to the transponder's memory. The transmitted radio waves are influenced by the tag because it reflects part of the energy. First, the unique identity and any other requested information are transmitted. In addition, different things can be stored.
The reader is a combination of hardware and specially programmed software. The more range a reader should have, the more energy in the form of electrical current must be used for its use. Typical ranges are between a few centimeters and a few meters. The smaller the range, the more precisely selected transponders can be addressed.
A longer range can be chosen, for example, if two objects should not be too close together. This is the case, for example, with containers containing flammable liquids and spark spraying equipment. Readers for radio frequency identification are available as handheld versions for manual operation, but can also take on various other forms, for example in the form of a gate through which goods flows.
Use of RFID in logistics 4.0
Hardly any other industry can profit as much from RFID and Auto-ID as logistics. Radio Frequency Identification perfects the Internet of Things through smart technology and therefore all object movements, which is why the use of RFID is of great importance for the Smart Factory. Logistics companies benefit above all from
- the acceleration of complex workflows,
- Simplified and streamlined databases with realistic inventory lists,
- easily trackable goods movements,
- reliable localisation of tagged objects,
- intelligent storage of goods and
- fully digital process logging.
As systems can almost manage themselves thanks to RFID, the need for human resources also decreases because the material flow can be fully automated(Auto-ID). This is probably the biggest disadvantage of RFID, because many jobs depend on logistics. Large pallets or even entire pallet trucks full of tagged objects do not have to be manually unloaded and scanned individually, but can be processed in a single step. Workers no longer have to manually check incoming and outgoing goods for type, quantity, origin and destination, because the RFID system clarifies these questions independently and loads all RFID data into the cloud. On the one hand, the error rate can be minimised and industrial communication can be established through the use of cloud technology.
Costs for RFID technology as auto-ID
Transponders, or tags, are relatively cheap to buy despite their great benefits. A single tag can be purchased for just a few cents. Depending on the equipment and functional repertoire, however, the price can increase many times over. On average, companies must expect costs of around 50 cents per day. But the more common RFID becomes, the cheaper the purchase price can develop. Unfortunately, RFID chips cannot be reused for other objects, since the identity always remains the same.
Misuse through unauthorised access
If strangers can get access, it may be misused. However, this is not an impossible thing, as the stored data can now be transmitted in encrypted form using appropriate transponders. This puts a stop to cybercrime in logistics. In addition, RFID transponders can be designed in such a way that only selected RFID readers have access to the stored information. Alternatively, passwords can also be set. Usually, the data is transmitted in plain text. However, the short range of the transponders, from a few centimeters to a few meters, provides a degree of protection against unauthorised access. Auto-ID therefore already provides good starting points for secure process control, whereby further development steps can certainly be worthwhile.
Weaknesses of RFID
The transmitting or receiving power of RFID systems can be disrupted, destroyed or interrupted. Possible causes are:
- Electromagnetic pulses (EMP),
- physical destruction of the transponder antenna (e.g. by simple cutting),
- Faraday cage and other forms of shielding (such as aluminium foil)
- interference transmitter with the same frequency as that of the tag
:quality(80)/images.vogel.de/vogelonline/bdb/1560700/1560730/original.jpg)
Digitalisation
Industry 4.0 clearly explained - Definition, benefits and topics
Prevent power outages
Like other Auto-ID technologies, RFID technology is dependent on electricity. While passive transponders do not use their own energy source and active ones usually use their own battery, readers can be connected directly to the power grid. Handheld readers often also use rechargeable batteries. The situation is not the same for permanently installed readers in logistics, which are used, for example, in warehouses. If there is a power failure, the reader of the radio frequency identification system will also fail. To prevent this, it makes sense to set up an automatic emergency power supply that also integrates RFID systems. However, data losses on described tags due to a power failure are not possible in this way.
Attacks on computer systems
As RFID systems become more common in business, they will become increasingly interesting for cyber criminals. To date, only scientists have been able to manipulate RFID chips to spy on databases. In this respect, it is worth keeping up to date at all times in order to offer cyber criminals as few targets as possible. In addition, the usual safety regulations, such as frequent updates and staff training, apply to computer systems related to radio frequency identification.
The History of Radio Frequency Identification
For the first time in human history, a pioneer of this technology was used in British military aircraft in the Second World War. It was used to automatically distinguish between British and non-British aircraft to avoid confusion with enemy aircraft. The main difference between the predecessors, which were about the size of a suitcase at the time, and the systems used today is the size and weight of the transponders. Modern transponders can be as small and light as a grain of rice, although there are still more massive tags.
In the 1960s, RFID found its way from the military sector into the economy and since then has played an important role for technologies in the field of Auto-ID. In this phase, it was mainly used to protect against theft. Shortly thereafter, the transceiver system was also used in agriculture to identify farm animals. Over the next few years, dozens of other areas of application were opened up. In the 1980s, RFID was found in toll systems. This development took place primarily in the USA and Norway. The system has been further developed and is not yet complete. RFID technology is now used in the economy, healthcare, retail, logistics, (tourist) infrastructure, blind care and many more.
And now it's your turn!
Give us feedback on this article. Which questions are still open, which aspects are you interested in? Your comment will help us to become better!
(ID:45890534)



:quality(80)/p7i.vogel.de/wcms/bb/74/bb74aefce7687b2ac87e62f6a52cf67e/0130170106v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/73/8a/738a9f20229e20ae938c5e690b37a5df/0129780274v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/d2/63/d26376330f084c718f9ab83fc66eb39f/0129319680v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/4f/a9/4fa94db21a092a12fdb0822e3d5c8150/0129504798v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/ec/86/ec86dc4bd5fd8425c4bc6fd71409e7ad/0131049990v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/32/16/3216bea996ced32365d17dcf41b9fd0f/0131076030v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/d1/ef/d1ef06600622f5bb2f3ce2676d68ec91/0131077323v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/60/45/6045cb15d71397154c6cee56d5d95ac7/0131063997v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/0d/6c/0d6c5ea88cb425ab9dd066457225e61b/0131066999v2.jpeg)
:quality(80)/p7i.vogel.de/wcms/03/41/0341f13be7d88e59075184138a9bfc44/0131010620v2.jpeg)
:quality(80)/p7i.vogel.de/wcms/16/fd/16fd246f520f6340c1d7fe77a26f817d/0130918842v2.jpeg)
:quality(80)/p7i.vogel.de/wcms/f5/ad/f5ad2cefc6d208da995f0768238e4537/0130726865v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/b2/73/b2735e537e1eb3efe40b5610b62e5cc3/0130952440v2.jpeg)
:quality(80)/p7i.vogel.de/wcms/b2/a3/b2a3109b76173f15093c53e031bc3b0f/0130927341v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/53/5f/535f333e84ac99d48506e145f564f7d7/0130933064v2.jpeg)
:quality(80)/p7i.vogel.de/wcms/9e/e1/9ee1377d9f07aef4a0bfdd76120777e9/0130750150v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/20/80/2080366dbf8cca84fe9d00659b8de85c/0131056632v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/44/b6/44b693400b1e32f96742addc69bd8d7c/0130946952v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/79/cf/79cf780f220d2f7119b8a8b0e33da14f/0130726885v2.jpeg)
:quality(80)/p7i.vogel.de/wcms/fa/61/fa6158da9810738698df5e753e618d65/0130636802v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/00/9a/009ae0e133b321f8f0dabfb3fe14d2a6/0130776695v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/28/43/28438c7998aebec0c2f5fb6f1a16b387/0130764478v2.jpeg)
:quality(80)/p7i.vogel.de/wcms/d1/5a/d15a3e1b3846c92e2ec610a5fb1f22dd/0130750258v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/68/41/684118d197bf027713cb709badbb3667/0130804377v7.jpeg)
:quality(80)/p7i.vogel.de/wcms/d5/1d/d51def0b31e213e756bbfb9479fa9c7e/0129925621v2.jpeg)
:quality(80)/p7i.vogel.de/wcms/f9/ca/f9ca9cace88200a5ec0946f193264963/0129209504v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/2f/61/2f61dd20be68049fa2320a2e5aa860d7/0123789183v2.jpeg)
:quality(80)/p7i.vogel.de/wcms/c5/49/c54973f28495dada1c7605f913717341/0121533734v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/76/aa/76aa92f11f136c10e16cc77a89a5f583/0131009272v2.jpeg)
:quality(80)/p7i.vogel.de/wcms/53/c7/53c73ae0a157d4c103e1964e77c1f425/0130023300v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/68/ab/68abf66929cb9f2dcb823a12e90d1d21/0129922525v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/46/85/46854ab7a2679db67354f556f2bc1db9/0129539660v2.jpeg)
:quality(80)/p7i.vogel.de/wcms/4c/dd/4cdd1643347d5f6f72743402d36e93f4/0130628083v2.jpeg)
:quality(80)/p7i.vogel.de/wcms/51/3e/513e2d937e96401a4d1ff8db1481cce7/0130242596v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/f8/8f/f88f47ba8e4ef50152497010c25dda11/0130168360v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/be/4d/be4da3d2f0d802d94127979ea4af68b4/0130748997v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/66/52/6652eb3a653a0908d5b03fb638f16260/0129646074v2.jpeg)
:quality(80)/p7i.vogel.de/wcms/9e/bd/9ebd826ceed28c644a9205bdbf82beb4/0131007997v2.jpeg)
:quality(80)/p7i.vogel.de/wcms/d5/e6/d5e68c74fabff18ef737ee767b7b359f/0130415707v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/6b/9c/6b9cab1e262f77caed8179ed3dc29807/0129104421v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/49/58/4958084fe5c4ed0a7758f7cfb3051e92/0128854986v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/ce/80/ce8008acc51e05d5c33a5890d07e239d/0131117485v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/e7/74/e774210496e99be6481defcde77bab19/0131116903v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/f7/8d/f78df2ee390561b7bca9624e430d6363/0130931883v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/9a/51/9a5199edfd0557c21666b29fafb56fc5/0130926622v1.jpeg)
:fill(fff,0)/p7i.vogel.de/companies/66/0e/660e93698db24/hasco-logo-or-b50.jpeg)
:fill(fff,0)/images.vogel.de/vogelonline/companyimg/84400/84424/65.jpg)
:fill(fff,0)/images.vogel.de/vogelonline/companyimg/118400/118496/65.jpg)
:quality(80)/p7i.vogel.de/wcms/79/6e/796ed7667040a5eab42246cbf7790510/0128162496v1.jpeg)
:quality(80)/p7i.vogel.de/wcms/3e/9b/3e9bc7a96b59079f96d7ad303d67e7b8/0125471933v1.jpeg)